Speakers for 2018
Confirmed speakers for CrikeyCon V
Gunter Ollmann
Keynote - Cloud Effects on Security Professionals: Attackers & Defenders
Public cloud, fundamentally changes the security equation for both attackers and defenders. Practically every piece of the cloud is instrumented, logged, and being analyzed at the network layer, host level, and everything in between – by default, all the time. For the attacker, there is no place to hide. One errant connection or detected compromise of a host anywhere in the cloud can quickly be blocked or inoculated throughout the rest of the cloud in seconds. For the defender, scale dictates that everything needs to be automated and exceptions may be manually handled once before being learned by an AI responder.
As a security professional, the cloud continues to modify our role in protecting our customers. The assets that used to be secured and managed by a customers small-team of self-learned defenders, are now protected by the latest advances in security technology; continually monitored and backed by several thousand fully trained professional defenders. Meanwhile, as cloud customers move from unicorn configured hosts, to herds of IaaS instances, and then migrate on to PaaS, SaaS, and eventually Serverless environments, “their” security obligations are transferred to the cloud operators. So what happens to all the 3rd-party specialist security service providers as public cloud dominates and consumes the enterprise?
Bio
Gunter Ollmann serves as CTO for Security and helps oversee the cross-pillar strategy for the Cloud and Enterprise Security groups. He has nearly three decades of information security experience in an array of cyber security consulting and research roles.
Before joining Microsoft, Gunter served as Chief Security Officer at Vectra AI driving new research and innovation into ML-based threat detection of insider threats. Prior to Vectra AI, he served as CTO of Domain Services at NCC Group, where he drove strategy behind the company's generic Top Level Domain (gTLD) program. He was also CTO at security consulting firm IOActive, CTO and vice president of research at Damballa, and chief security strategist at IBM, and built and led several well known and respected security research groups around the world - such as X-Force. Gunter is a widely respected authority on security issues and technologies and has researched, written and published hundreds of technical papers and by-lined articles.
Originally, Gunter had wanted to be an architect but he lost interest after designing retaining walls during a three-month internship. After that, he qualified as a meteorologist, but was lured to the dark side of forecasting Internet threats and cyber attacks. His ability to see dead people stoked an interest in history and first-millennium archaeology.
Scotty Brown
Our lovely MC
Peter Hannay, Clinton Carpene & Jack Turner
Let’s Play-AI Super Metroid.
Machine learning is cool right now. Whether you’re an AV firm struggling to detect meterpreter, a CIO for an ICO working out how you can legitimately work the terms “machine learning” and “blockchain” into the same sentence, or developing a robot that doesn’t walk itself into a pond, AI and machine learning is hot on everyone’s minds.
In this talk we explore the basics of machine learning, exploring the general functionality of machine learning algorithms, how they work, and how they are (mis-)used. You will see first-hand our struggles to achieve our dream, to build an AI that can play videogames for us. We are determined to live the dream of never having to play video games again and we want that for you too!
Bio
Peter Hannay is a lecturer and researcher based at Edith Cowan University in Perth Western Australia. In addition, Peter is an organiser of WAHCKon and generally cool guy.
Clinton Carpene is a reformed academic that hacks for a living as a penetration tester for Asterisk Information Security in Perth. Clinton is also an organiser of WAHCKon and SecTalks Perth.
Jack currently works as a pentester for Asterisk Information Security in Perth. He contributed a challenge to the recent WACTF and previously competed in the CySCA challenge for ECU. He has recently taken an interest in binary exploitation and reverse engineering, and in his spare time enjoys flying planes without engines.
David Jorm & Brendan Scarvell
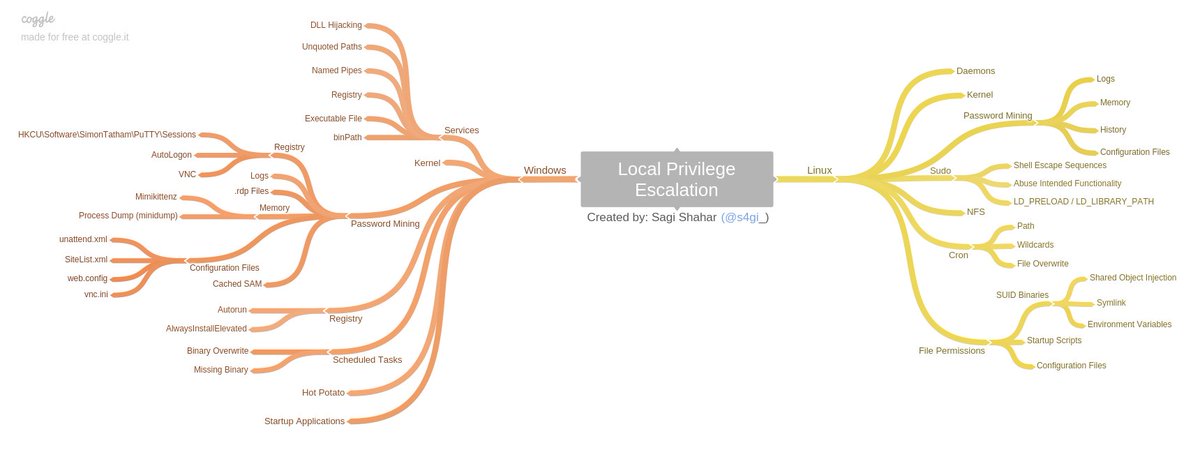
Analyzing Java Heap Memory Dumps
During a recent penetration test, we identified a vulnerability that allowed us to download a full heap memory dump from the application server. This presentation will examine the vulnerability itself, the structure of the heap dump, and the tools available for analysing it. Using a sample application, we will show the potential to extract critical information from such a memory dump, and provide some ideas for future research.
Bio
David and Brendan work for Trustwave SpiderLabs as part of the Asia-Pacific penetration testing team. They are both working towards the goal of jetski ownership, as this is a customary milestone of success in the Australian InfoSec industry.
Joshua Graham
Vulnerability Research for the Skillless: Substituting Experience with Persistence (or How I learned to Stop Worrying and Find UXSS/RCE)
In my first year in information security I got obsessed with a couple of little bugs…and after following said bugs down the proverbial rabbit hole ended up with novel RCE in SQL and UXSS in Microsoft Edge.
MySQL/Maria DB are now patched and Edge is due to be patched in January. The talk will take the audience on a journey from discovering an innocent looking bug and through the process of understanding what is causing the bug and the lateral thinking used to result in big bugs. The talk will include a live demonstration + a little Autohotkey.
Bio
Joshua has a background in general IT and software engineering. In late 2016, through a series of unfortunate accidents, he joined TSS as a full time penetration tester and fell in love with the security world. His hobbies include opening popup windows in various browsers, AutoHotkey and MS Paint.
He has achieved formal qualification training through Offensive Security Penetration Testing with Kali security course and holds a bachelor of information technology majoring in software engineering.
He was also a part of the winning capture the flag team at Ruxcon 2016, 2nd place team at Kiwicon 2016 and 4th place team at Ruxcon 2017. Joshua is an active security researcher with CVEs in high profile applications such as MySQL and Microsoft Edge and is also a vocal member of the Brisbane security community having created CTF challenges and presented at the Brisbane Sectalks meetup.
Catherine McIlvride & Fiona Sasse
Pizza Roullette
Catherine and Fiona are security newbies in the world of bleepbloops. As their hunger for more knowledge on Security Testing grows, they attempt to chomp into the cyber realm of ordering pizza. Pull up a chair, grab a slice* and prepare yourself for a feast!
* Disclaimer: Pizza will not be included.
Bio
Catherine and Fiona are software testers who have been united by their passion for pizza and their curiosity for wearing black and white hats. They hammer and chisel their way through interfaces, databases, and all other places to identify cracks and gaps. Now they face their next adventure roaming unfamiliar territory in the security space.
Kylie
How to (un)route your network
Communication across the network is core business for most organisations and in fact the entire Internet. But what happens when a hacker messes with the interconnects we rely on? This talk will overview vulnerabilities known in popular routing protocols. The presentation will explain how the protocols work and demonstrate the effectiveness (or not) of the vulnerabilities.
Bio
Kylie is currently an Emerging Technology Researcher and Security Architect. She is responsible for leading applied research into emerging technologies as well as developing and providing security architecture advice to early adopters. Kylie studied Telco Engineering at ANU in the late 90s, has a Masters in Computer Networking with CSU, several industry qualifications and is also an adjunct lecturer with UNSW Canberra. She is the co-organiser of BSides Canberra and co-owner of Canberra’s hackerspace - InfoSect. Kylie has previously presented at the Australian Cyber Security Centre (ACSC) conference, BSides Canberra, WAHCKon and Christchurch HackerCon (CHCon).
Clinton Kerrison
Putting the MITM in HDMI(tm)
The presentation will centre on the demonstration of a HDMI and USB HID MITM dropbox for client site assessments, with some history of the different versions of the project.
Bio
Clinton is an experienced end user troubleshooting and support consultant, with 4 years of experience operating an in-home computer consultancy and a Junior Security Consultant with Alcorn Group.
Fraser Tweedale
Open Source user session recording
In this presentation we will discuss the limitations of existing Open Source approaches, then present the Scribery project, an end-to-end session recording solution with features including:
- Terminal session playback and real-time monitoring (including what the user sees)
- Centralised storage and correlation with auditd log events
- Centralised control of what or whom to record, via SSSD and in the future FreeIPA
- Cockpit integration
The presentation will include a demo of a user session being recorded, stored centrally, inspected and played back.
We will look at the architecture, discuss implementation challenges, and conclude with an overview of the road ahead.
The intended audience is system administrators and security officers responsible for security and compliance, and developers of security, identity and policy management systems.
Bio
Fraser works at Red Hat on the FreeIPA identity management system and Dogtag Certificate System. He's interested in security, cryptography, functional programming, type theory and theorem proving. Jalapeño aficionado.
Eric Pinkerton
Red Team Black Bag Golden Ticket or White elephant?
In this talk I will explain some of the many tools and techniques of the fascinating field of red teaming physical security and give you my own thoughts on what is actually useful versus what is a complete waste of money and space.
Bio
Eric has been breaking things just to fix them again since he was five, at 20, he spent his summer evenings working the door in a nightclub, and reading tarot cards during the day.
He didn’t realise it back then, but nothing could have prepared him better for a career in InfoSec.
Cutting his teeth in the last century working as a technologist for the BBC World Service in London Eric developed a passion for emerging technologies, with a particular bent for security.
Arriving in Australia in 2003 he landed an operational role at Australia’s first IP Telco, Comindico, before moving to Telstra, then Stratsec (acquired by BAE Systems), CSC and Finally Hivint.
He has presented at Cebit, AusCERT and AISA, AusNOG and Crikey he remains a healthy sceptic who is still partial to aluminium millinery, he blogs about privacy, security and the myth of infallibility in humanss.
Mark Piper
CT Logs are the new Black
This talk is the result of a small personal side project for better understanding CT logs and how they may be used. It resulted in crunching some decent sized data sets (numerous terabytes of compressed data) to extract certificate data relevant for work in NZ & AU, contemplating this datasets use and relevance for both blue and red teams.
We will examine a series of basic questions such as; What are CT logs? What is stored in the logs? How can we access and query these logs? How is any of this useful for attackers and defenders alike?
Bio
Officially hired as a Network Ransacker; Pipes spends his days looking at applications, executing red teams and generally musing about security for Insomnia Security.
While his current location is somewhat transient, he finds it pretty hard to resist a trip to Queensland each Summer.
Nicole Becher
Cyber Insurance
The market for cyber insurance is expected to reach $14 Billion by 2022. Many companies, large and small, have purchased it already or are in the process of evaluating. Technical information security professionals are being asked to participate in this process with little to no background information on the commercial insurance industry as a whole, and more specifically the cyber insurance market.
Many insurance carriers are piling into the market but is there a lack of real and valuable data are they instead focused on increasing market share and profitability. Cyber insurers need to focus on pricing this risk correctly, otherwise the financial risk could devastate market participants. What data would be more useful for cyber insurers to better understand, price and write this risk?
This talk will explore an (hopefully not boring) overview insurance industry as a whole, specific cyber policies that are currently being written, how this risk is priced, what data would be more useful for insurers to use to underwrite and an overall focus on what cyber insurance can do for the cyber security industry as a whole.
Bio
Nicole Becher is professional information security consultant. She has been in the cybersecurity space for over ten years working mainly in offensive security capacities. She manages penetration testing and red teams, forensics and incident responders, and malware reverse engineering team. She has also worked on cyber policy for New York State Department of Financial Services, where she helped develop the first-in-nation regulatory framework for assessing the cybersecurity of large and complex financial institutions.
She also help draft the first-in-nation regulatory and licensing framework for bitcoin and virtual currencies. Nicole is also as an Adjunct Instructor at New York University (NYU), where she teaches courses on offensive and defensive computer security, network security, web application security, and computer forensics. She is a chapter leader for OWASP Brooklyn (Open Web Application Security Project) and the project leader for OWASP’s newest project, DevSlop.
Nicole has presented both talks and trainings, at various conferences around the world on topics related to her research interests. These include web application and API security, malware analysis techniques, economics of cybersecurity, cyber insurance, cybercrime, and international cyberlaws and regulation. She has also advised Hollywood scriptwriters on cybersecurity and hacking. Nicole is on the SMART Conservation Technology Security Council, working to improve the security of animal and environmental conservation.
She is a Cybersecurity fellow of New America, a Washington DC-based think-tank, and is a fellow of the Madison Policy Forum, a cybersecurity-focused policy group bridging military, government and industry. She is a Certified Information Systems Security Professional (CISSP).
Alex
Operation Luigi: How I hacked my friend without her noticing
Yep so I asked my friend if I could hack her and she said yes. This is about what worked, what went wrong, all the flubs I made, and how to not suffer the same fate as her.
Also Mario's green brother is there, and then that part takes a sinister turn.
Bio
Alex is a blue teamer, magician, sweet mango boy, five-time celebrity masterchef winner, and a certified Luigi Technician.
Critics have described him as "aggressively wonky". You can find his internet antics at https://mango.pdf.zone.